Progress Report #29
19 April 2026
This Progress Report summarizes developments in Chaocipher research,
publications, and historical discoveries since Progress Report #28
(January 2023).
Here's a table of contents for this report:
Chaocipher and Cryptology
Byrne Genealogical Information
Chaocipher and Cryptology
A
Chaocipher Challenge Message on Reddit
In July 2020, Reddit poster YaF3li presented several
cipher challenge messages. Challenge message #4 is
a Chaocipher-encrypted message. Originally, only the
ciphertext was provided. The author soon expressed doubts about the
fairness of the challenge ("It
is Chaocipher, but the length of the ciphertext might be too short to
solve, I'm not sure. If so, let me know. I just found the thing
fascinating, that's why I included it."). To
address this, he later added the plaintext.
Here is a good challenge for Chaocipher analysts: given the
ciphertext and corresponding plaintext, can you deduce the left and
right alphabets used to encipher the plaintext?
Ciphertext:
RWTJQ CBRAN SDDIJ IWPMT XTSSM BPQWW
QLHTG ATWNL CZCHH WXSYS KEYZV ZITCA HZPZE QNBXT YQCBB VOBBI
WTTWE GVCVE RLVUH XJXHT BEMPZ VONCX
JPQRN BXTIK GBPQQ ZHPWX XELXA LFPXY KZYDS FAWNP WEOHO EPDVQ
FFOGE RHZSP XRJLK BIKIU APPRN ILKSQ
OTQPM GCAKK JJ (202 characters)
Plaintext:
OKAY SO THIS IS JUST A TEST BASICALLY
BECAUSE I HAVE NO IDEA WHETHER THIS IS SOLVABLE GIVEN THE
RELATIVELY LITTLE AMOUNT OF CIPHERTEXT
HERE AGAIN THE REST HERE IS PADDING SO IT IS AT LEAST A
LITTLE LONGER IN THE HOPE THAT THIS
HELPS WITH DECRYPTION (202 characters)
William
F. Friedman mentions Byrne to Henry Langen in a letter
Henry
E. Langen was the Editor of the American Cryptogram
Association between the years 1952-1956. Although a
cryptographic amateur, he brought energy to his position
and wrote many columns in The Cryptogram to spur interest in
the hobby.
Langen is connected to Chaocipher due to John F. Byrne's paying
him a visit in May 1954, during which they discussed
Chaocipher. Byrne misled Langen by claiming he had a working
demonstration model, apologizing that it was too heavy to bring. In
reality, no such functional model existed; only a wooden prototype with
movable tiles.
On the NSA site one can read a letter
from William F. Friedman to Langen, dated June 1954.
In the letter, Friedman acknowledges whatever Langen wrote
him about Byrne. Friedman was not interested in Chaocipher,
and only replied "Your mention of Mr. Byrne reminds me that I gave a
brief review of his book before a local group devoted to the
study of James Joyce. I had a very interesting time and I
hope my audience did, too."
Publications
that mention Chaocipher
Academic publications are citing the Chaocipher with increasing
frequency. Researchers are analyzing its structure, comparing it with
other encryption methods, and incorporating it into diverse areas of
study. The cipher is gradually moving from historical curiosity to a
recognized topic in contemporary cryptologic
research. Following are several such publications
Publication:
Steganography and Cryptography Inspired Enhancement
of Introductory
Programming Courses
A paper titled "Steganography
and Cryptography Inspired Enhancement of Introductory
Programming Courses" (Yana Kortsarts and Yulia
Kempner) was published in the July 2015 issue of Information Systems
Education Journal. As their abstract says:
Steganography
is the art and science of concealing communication. The goal of
steganography is to hide the very existence of information exchange by
embedding messages into unsuspicious digital media covers.
Cryptography, or secret writing, is the study of the methods of
encryption, decryption and their use in communications protocols.
Steganography manipulates data to ensure the security of information,
but the concept of steganography differs from cryptography.
Cryptography obscures the meaning of a message, but it does not conceal
the fact that there is a message. The goal of cryptography is to make
data unreadable by a third party, whereas the goal of steganography is
to hide the data from a third party. We present a way to integrate
steganography and cryptology examples into introductory programming
courses. This enrichment promotes active involvement in the course and
provides opportunity to engage students in experimental problem solving
and collaborative learning to enhance critical thinking.
On page 28, the authors bring Chaocipher as an example of a dynamic
substitution cipher:
Dynamic substitution cipher -
Chaocipher
Recently, we also integrated into the course curriculum, a less known
and more complex cipher, chaocipher, (Byrne, 1918; Rubin, 2010),
belonging to the group of dynamic substitution ciphers. [. . .] In our
approach we closely follow the description of the algorithm published
in July 2010 by Moshe Rubin (2010), providing further adaptation and
clarifications for novice programmers. [. . .] To ease the transition
and increase the difficulty level gradually, we first permit students
to use additional array/list storage, increasing the space complexity
of the algorithm. As a complete implementation, students are required
to implement all these array/list manipulations with minimal additional
space usage. To avoid any attempts at plagiarism, we provide only
cipher description and all necessary details to design a computational
implementation. We emphasize the mystery around this cipher to keep
students motivated and excited. We reveal the name and history of the
cipher only after students complete writing the program, but before the
collaborative testing step of the assignment. The mystery around this
cipher and the interesting history attract students’
attention. This cipher provides an opportunity to practice complex
manipulations of one- dimensional arrays and lists data structures,
utilizing a wide range of built-in Python lists methods and functions,
and writing custom functions in C. From the best of our knowledge, this
cipher is not covered in any cryptography textbooks.
Publication:
Digital Signature on Digital Images using the Least Significant Bit
Algorithm and the Chaocipher (Indonesian)
The paper "Digital
Signature on Digital Images using the Least Significant Bit Algorithm
and the Chaocipher" (Siwabessy, 2016) is a Bachelor of
Computer Science submission written in Indonesian.
Translated from the abstract:
Documents
in the form of digital image has the possibility to be manipulated
unlawfully. The information contained within can be faked, so that the
recipient of the document can be wrong in interpreting the intention of
the information therein. This could result in losses for both the
sender and recipient document, the decision made, based on the
information that has been falsified. A solution is needed to secure the
information stored on it. Information from the sender must be the same
when it reached the receiver. In this study generated digital signature
applications implemented in a way that is calculating the value of
bytes of data into a form MD5 hash algorithm. Results hash is then
encrypted with an algorithm Chaocipher. Cipher hash then inserted at
Least Significant Bit of digital images. Digital signature is inserted
can be used to detect whether the digital image has been changed or
not. The test results showed that the change can be detected, even if
the change only by 2x2 pixels.
It is encouraging to see Chaocipher gaining traction in academic
research, not only as a historical artifact but as a system that
continues to inspire analysis and experimentation.
Publication:
Analyzing and Creating Playing Card Cryptosystems
Isaac Reiter is the author of the 2020 paper "Analyzing
and Creating Playing Card Cryptosystems", submitted
in as an honors mathematical paper at the Kutztown University
of Pennsylvania. In this paper, Reiter proposes a new
card-based cryptosystem. This proposed system incorporates
features from the Card-Chameleon and Chaocipher playing card
cipher systems and improves on them.
From the abstract:
Dr. Landquist and I spent the
summer of 2019 examining existing playing card
ciphers. This led to the main focus of this paper: the creation of a
unique, secure
playing card cipher. Because of the inspiration provided by the cipher
VIC, I am
calling our original cipher VICCard. VICCard has gone through multiple
versions,
each better than the last. Its security is rooted in its combination of
numerous cryptographic principles, including a substitution
checkerboard, columnar transpositions,
lagged Fibonacci generators, and junk letters. As evidenced by certain
randomness
tests, VICCard has the potential to extensively randomize an English
plaintext.
Regarding Chaocipher, Reiter writes (page 8):
Second, Chaocipher is a
cryptosystem that was created by John F. Byrne in 1918. Although
Chaocipher has been around for over a century, the disclosure of the
Chaocipher algorithm occurred as recently as 2010. As he was examining
previously invented playing card ciphers, Toponce had the idea of
adapting the Chaocipher algorithm to playing cards. Given the
respectable security of Chaocipher, I did not find a weakness that was
as severe as that in Card-Chameleon. The closest thing to a weakness is
the existence of plaintext/ciphertext pairs (or pt/ct pairs). A pt/ct
pair is when two identical plaintext letters encrypt to the same
ciphertext characters, such as two a’s encrypting to two
o’s. Greg Mellen noticed that when he divided messages
encrypted by Chaocipher into blocks of 13 letters, pt/ct pairs rarely
occurred within these blocks. Moshe Rubin hypothesized
that pt/ct pairs will only occur if the two plaintext letters are
separated by a distance of eight letters. In order to put
a rest to this question, I wrote a program that took two a’s
and tried every 1-letter, 2-letter, 3-letter, 4-letter, and 5-letter
combination between these two a’s. After testing all
12,356,630 of these cases, the program did not find any pt/ct pairs. However, it did find
pt/ct pairs with certain 6-letter combinations. As a result, we can say
for certain that at least six letters must be between two plaintext
characters for a pt/ct pair to occur.
Two clarifications should be made here:
- The paragraph contains an inaccuracy: the text should read "Moshe Rubin hypothesized that
pt/ct pairs will only occur if the two plaintext letters are separated
by at
least a
distance of eight letters." This appears to be
what the author intended.
- Reiter is to be credited with empirically showing that the
minimal number of intervening letters between identical pt/ct
pairs is six (6), as he explains in the paragraph. At the
same time (also in 2020), Moshe Rubin proved
this identical result mathematically.
Publication:
Code Complexity Overview, and an Analysis for Various Programming
Languages
The paper, Code
Complexity Overview, and an Analysis for Various Programming Languages,
by Cameron Reid (2024), evaluates the algorithmic complexity of a wide
range of programming tasks using a custom metric. Chaocipher receives a
score of 6.351905, placing it among moderately complex tasks such as
matrix‑chain multiplication and bounded knapsack.
From the abstract:
Software
complexity is notoriously difficult to measure, but can have a profound
impact on the performance of a software development team and the
continuing robustness of a software product. Significant effort has
been made for many years to attempt to measure software complexity, as
this is a problem that can have significant financial impact. Software
that is too complex may also be too difficult to modify, understand, or
debug. Meanwhile, the problem of designing a programming language can
be understood as optimizing a utility function which balances
performance with simplicity. In this work, I will attempt to explore
some proposed methods for measuring software complexity and examine how
the choice of programming language can impact the complexity of a piece
of software.
Following is a partial table of task complexity metrics, including
Chaocipher's score of 6.351905. It should give you an idea of
the range of complexities:
| Task |
Mean Complexity |
| Shell-one-liner |
0.045517 |
| Halt-and-catch-fire |
0.216667 |
| Hello-world-Text |
0.298814 |
| Hello-world-Standard-error |
0.326364 |
| Literals-Floating-point |
0.327647 |
| Include-a-file |
0.363902 |
| . . . . |
|
| Inverted-syntax |
1.000417 |
| HTTPS |
1.028065 |
| Increment-a-numerical-string |
1.047647 |
| Secure-temporary-file |
1.076923 |
| Simulate-input-Mouse |
1.103636 |
| Loops-Foreach |
1.104643 |
| . . . . |
|
| Iterated-digits-squaring |
5.037143 |
| Ramer-Douglas-Peucker-linesimplification |
5.041875 |
| Morse-code |
5.048800 |
| Numbers-which-are-not-the-sum-of-distinct-squares |
5.049000 |
| Shortest-common-supersequence |
5.055833 |
| Safe-primes-and-unsafe-primes |
5.070870 |
| IBAN |
5.078462 |
| Levenshtein-distance |
5.106383 |
| . . . . |
|
| Permutations-Derangements |
6.217000 |
| Long-multiplication |
6.325294 |
| Matrix-chain-multiplication |
6.330417 |
| Knapsack-problem-Bounded |
6.346364 |
| Chaocipher |
6.351905 |
| Perlin-noise |
6.420714 |
| Periodic-table |
6.445556 |
| Koch-curve |
6.448750 |
| . . . . |
|
| Snake |
19.191875 |
| Peaceful-chess-queen-armies |
20.200588 |
| Hunt-the-Wumpus |
20.332667 |
| One-time-pad |
20.565000 |
| Rare-numbers |
22.071579 |
| P-Adic-square-roots |
24.320000 |
| K-means++-clustering |
25.553333 |
| P-Adic-numbers-basic |
26.784000 |
| P-value-correction |
28.286000 |
| Minesweeper-game |
31.507647 |
Publication:
The true and the real: Joyce’s ‘world‑likeness (in
Hungarian)
 I came across the
following paper (2024), written in Hungarian, titled "The
true and the real: Joyce’s ‘world‑likeness".
Written by András
Kappanyos, the author is a Hungarian literary historian,
translator, and university professor. His paper relates to
John F. Byrne, his relationship with Joyce, and Byrne's Chaocipher.
I came across the
following paper (2024), written in Hungarian, titled "The
true and the real: Joyce’s ‘world‑likeness".
Written by András
Kappanyos, the author is a Hungarian literary historian,
translator, and university professor. His paper relates to
John F. Byrne, his relationship with Joyce, and Byrne's Chaocipher.
Copilot AI Summary of the
Paper
I asked Copilot AI to summarize Kappanyos's paper. Here is
its summary.
The study examines how
James Joyce built his narrative universe almost entirely from real
people, places, and events he observed in Dublin before leaving Ireland
at age 22. Rather than inventing stories from imagination, Joyce
treated memory as his creative engine, transforming lived experience
into literature. The document shows how Joyce’s
works—from the early epiphanies through *Dubliners*, *A
Portrait of the Artist as a Young Man*, *Ulysses*, and *Finnegans
Wake*—reuse, refine, and recombine autobiographical material,
gradually compressing and stylizing it into a coherent fictional world.
As the author notes, Joyce “22 éves
koráig emlékeket és
benyomásokat gyűjtött Dublinban, majd
élete hátralévő
részében… irodalommá
dolgozta át ezeket” (“until age 22 he
gathered memories and impressions in Dublin, and spent the rest of his
life turning them into literature”).
A major focus of the document is Joyce’s three key
contemporaries—Stanislaus Joyce, John Francis Byrne, and
Oliver St. John Gogarty—whom Joyce metaphorically called his
“grindstones”
(“köszörűkövek”). Each
man influenced Joyce intellectually and personally, and each later
wrote his own account of their shared past. These memoirs, written
after Joyce became famous, attempt variously to clarify, correct, or
counter Joyce’s fictional portrayals. Byrne, for example,
recounts how he helped Joyce through a personal crisis in 1909 and
later published *Silent Years*, where he describes both Joyce and his
own invention, the Chaocipher: “Memoárja 1953-ban
jelent meg Silent Years címmel…
főművének pedig a Chaocipher…
rejtjelezési eljárást
tartotta.”
The final section contrasts Joyce’s fiction with these
alternative narratives. While Stanislaus and Byrne generally support or
contextualize Joyce’s versions of events, Gogarty’s
fictionalized memoir *Tumbling in the Hay* attempts to undermine
Joyce’s self‑presentation by depicting his alter ego as
insignificant and directionless. Yet the document argues that
Joyce’s narrative universe ultimately supersedes these
competing accounts: his fiction is “valósabb, mint
ami ‘valójában
történt’” (“more real
than what ‘actually happened’”).
Excerpt:
Chaocipher-Related Paragraph (Page 17)
Here is a translation of the section relevant to Chaocipher:
"After 1909, Byrne met Joyce
two more times: in 1927 and in 1933 he visited the family in Paris,
spent a few days with them, and besides reminiscing about old times
they talked about new sections of Finnegans Wake.
His memoir was published in 1953 under the title Silent Years.
Byrne worked mostly as an economic journalist in New York, and he
regarded the cryptographic method called the Chaocipher as his major
life’s work. Joyce was an important figure in his life, but
by no means the central one. When, in the early 1950s, he brought the
manuscript of his autobiography to a New York publisher, he himself did
not really know how significant it would be for the by‑then already
very lively field of Joyce scholarship. It was almost certainly the
publisher who suggested that James Joyce’s name should appear
at least in the subtitle of the book, since for potential readers this
would provide a much more likely point of connection than the
cryptographic method demonstrated with numerous examples —
but in reality Joyce’s name appears in at most half of the
chapters. In those places, however, Byrne undoubtedly plays into the
hands of the philologists: like Stanislaus, he also recounts how
certain scenes actually happened in real life, some of them not even
with Joyce, but with Byrne himself."
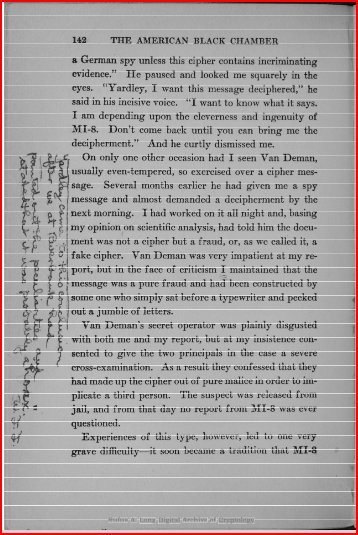
William
F. Friedman's version of the Yardley-Damen story
This item adds historical perspective to Byrne's contacting Herbert O.
Yardley in 1958. To understand the background, here is an
excerpt from my 2011 paper in Cryptologia, "John
F. Byrne's Chaocipher Revealed: An Historical and Technical Appraisal",
pages 336-337:
A reader would be excused for understanding that Yardley had performed
the commendable analysis on his own.
It turns out that William F. Friedman had a different version.
In Friedman's
copy of Yardley's "American Black Chamber", on page 142 where
the story is told, we find the following comment in the margin:
"Yardley came to this conclusion
after we at Riverbank had pointed out the peculiarities and stated that
it was probably a hoax. W.F.F."
According to Friedman, Yardley repeatedly took credit for cryptanalytic
work that had actually been performed at Riverbank Laboratories -- much
of it by Friedman himself or under his direction. During the period in
which Yardley was associated with Riverbank, Friedman was building what
would become one of the most capable cryptographic research groups in
the United States.
Friedman’s anger toward Yardley, however, went far beyond
questions of credit. His criticism was deep, sustained, and rooted in
professional ethics as well as national‑security concerns. He regarded
The American Black Chamber as a reckless and damaging disclosure of
U.S. cryptographic capabilities. His reaction took many forms:
extensive marginal notes in his personal copy of the book, formal
complaints within government channels, and increasingly hostile
correspondence with Yardley.
Friedman’s objections can be understood in four overlapping
dimensions:
• Ethical - Yardley violated
the professional secrecy that cryptanalytic work required.
• Operational - The book
jeopardized ongoing and future U.S. intelligence efforts.
• Personal - Friedman felt
betrayed by a former colleague who had once been part of the same small
cryptologic community.
• Documented - His disapproval
survives in annotated books, letters, and official memoranda.
The archival record -- especially Friedman’s heavily
annotated copy of The American Black Chamber -- offers a uniquely
detailed view of his disapproval. The marginal comment quoted here is
only one of many such notes that reveal the depth of his frustration
with Yardley’s actions.
"Coded
Insights" Website: The Chaocipher
This
website attempts to summarzie the history of Chaocipher.
The site succeeds in capturing the history accurately,
although lacking in references and links to resources.
Video
game "Keep Talking and Nobody Explodes" highlights Chaocipher
In Progress Report #27, I wrote about a website
that referenced Chaocipher that completely baffled me.
I couldn't figure out who was referencing Chaocipher in what
looked like an online game.
I was therefore delighted to receive an email in February 2025 from
someone with a handle of "Timwi" who kindly explained the context.
Below is our correspondence, which sheds light on how
Chaocipher appears in the KTANE modding community.
1
February 2025: Timwi to Moshe Rubin
Hi!
I randomly stumbled upon your Progress Report #27
where you ask: “What does this reference here to Chaocipher
mean?”, linking to this page titled “On the
Subject of Ultimate Cycles”.
What you have found here is
a document relating to a video game called Keep Talking and
Nobody Explodes (website | Wikipedia). The game has a
fan-run modding community of programmers who make
“modules” (minigames/puzzles) for the game. Several
of those fan-made modules deal with encryption ciphers.
The game consists of a
“bomb” that must be “defused”,
which really means to solve the modules (puzzles/challenges) on it
within an allotted amount of time (before the bomb
“explodes”). The player holding the bomb (the
“defuser”) will relay information displayed on the
modules to the other players (the “experts”) who
use manuals such as the one you discovered to
“disarm” (solve) each module.
There are in fact three
separate modules that involve Chaocipher. They are:
- Ultimate Cycle (manual | Steam Workshop), created by
SpeakingEvil — this is the one you discovered
- Cream Cipher (manual), part of a module
pack called Colored and Ultimate Ciphers (Steam Workshop), created by
Sean Obach
- Cipher Machine (manual | Steam Workshop), also
created by Sean Obach, which is so extensive that each cipher has its
own manual, including Chaocipher
I hope I was able to clear
up your confusion!
Timwi
4
February 2025: Moshe Rubin to Timwi
Dear Timwi,
First and foremost, thank
you for taking the time to contact me. Reading your reply and
browsing to your links, I now realize there is a whole world of
fascinating "Keep Talking and Nobody Explodes" enthusiasts out there -
and to think I had no idea <g>. I just watched
the video https://steamcommunity.com/app/341800/videos/
and was sitting on the edge of my seat!
With your permission, in the
upcoming Chaocipher Progress Report, I would like to highlight your
email and write about the KTANE community.
Thank you so much for taking
the time and energy to update me. You are a true
professional!
Best regards,
Moshe Rubin
Jerusalem, Israel
Maintainer of the chaocipher.com website
4
February 2025: Timwi to Moshe Rubin
Thank you for your kind
words! Yes, you have my full permission to publish the e-mail that I
sent you, and to link to and describe KTANE including my repository of manual pages.
I should note that the
videos you saw on Steam are quite old. KTANE started out (and is still
marketed as) a party game; the modules in the base game are easy once
you understand them and the novelty value wears after a while. The
modding community has taken the game way into the stratosphere by
creating modules that are way harder, far more serious and more
elaborate. One reasonably well-known proficient defuser in the
community is Zefod42
on YouTube who has uploaded many videos of their successful
defusals of large bombs that include more modern, difficult modules.
Most of his videos are showing the defuser side, but here’s
one where he’s the expert and you can see him deal
with manuals and calculations and all the gritty stuff.
Another way that you can get
an idea of how KTANE modules work is by looking at tutorial
videos that fans of the game have made to explain them.
Here’s a
tutorial video for Cream Cipher and here’s
one for Ultimate Cycle, two of the
modules that I mentioned that include Chaocipher in their gameplay. The
third one, Cipher Machine, is so extensive that the
tutorial video doesn’t cover all of it.
Fun talking to you!
Timwi
This exchange opened my eyes to the vibrant KTANE modding community and
its creative use of Chaocipher. It is remarkable to see the cipher
appear in such an unexpected modern context.
Chaocipher
in Klaus Schmeh's "Codeknacker gegen Codemacher" (Codebreakers against
Codemakers)
Klaus Schmeh is a German computer scientist and one of the
world’s most prolific writers on cryptology. He has authored
numerous books, articles, and papers, and is widely recognized for his
accessible writing on historical and modern encryption.
It was therefore with great interest that I ordered his German language
book, "Codeknacker gegen Codemacher" (Codebreakers against Codemakers).
Schmeh covers the Chaocipher system on pages 237-240, which I
have translated using Copilot AI. The following is
Schmeh’s interpretation of Byrne’s work. While his
narrative is engaging, it includes several evaluative statements that
reflect his own perspective.
Chaocipher:
A
90-Year-Long Misunderstanding
In
James
Joyce’s novel Portrait of the Artist as a Young Man,
there is a protagonist named “Cranly.” The model
for this fictional character
was Joyce’s friend and fellow student John Byrne
(1880–1960). This John Byrne
entered the history of cryptology by inventing an encryption device
that
occupied him and many others for decades: the
“Chaocipher” (Rubin, 2011).
Unfortunately,
Byrne did just about everything wrong that he could have.
He barely engaged with the fundamentals of cryptology yet considered
himself
clever enough to develop a revolutionary encryption method. He vastly
overestimated the quality of his Chaocipher and even believed it to be
unbreakable. He kept the workings of the Chaocipher secret until his
death,
although the security of a method should never depend on its secrecy.
In other
words: Byrne was the embodiment of the Dunning-Kruger effect.
Byrne,
who
emigrated to New York in 1910, invented the Chaocipher in
1918. Until then, he had little to do with cryptology. He revealed that
the
otherwise secret mechanism of his device was a relatively simple
construction
that fit entirely into a cigar box. The Chaocipher thus competed with
devices
like the Enigma or the Hagelin machines—a hopeless endeavor.
Byrne
offered
his invention to several U.S. agencies, including
cryptology genius William Friedman, who examined the method. But no one
wanted
the Chaocipher. None of the experts pointed out its
weaknesses—a common tactic
when one wants to keep their expertise to themselves. Some reviewers
even gave
moderately positive feedback. This was likely strategic: even stating
that a
particular encryption device was poor could be valuable information to
an
adversary. But Byrne didn’t see through this and continued to
believe he had
invented something extraordinary.
Byrne
invested
a lot of time in the Chaocipher. Like many figures in
cryptology history, he was multi-talented and curious. In his youth, he
was one
of Ireland’s best chess players and later became a respected
journalist. It
probably would have been better to focus on those pursuits, but the
Chaocipher
was more important to him. In 1953, Byrne published his autobiography Silent
Years, citing the Chaocipher as the main reason for the book.
He still
didn’t reveal how the method worked but published numerous
encrypted texts
along with their plaintexts. He even offered a $5,000 prize to anyone
who could
crack the messages within three months. Byrne died in 1960 without
receiving
the recognition he had hoped for.
In
1973,
crypto-historian Louis Kruh was looking for interesting topics
for a cryptology event and came across the Chaocipher. Since John Byrne
was
long deceased, he contacted Byrne’s son, John Byrne Jr., who
was well
acquainted with the workings of the Chaocipher. Like his father, he
refused to
reveal anything about it. He also overestimated the method’s
quality and hoped
to commercialize it—even though electronic encryption
machines already existed.
Kruh
remained
in contact with Byrne Jr., and in late 1989, the latter
finally made a concession. Kruh and his colleague Cipher Deavours were
allowed
to examine the device. They later expressed cautious approval of the
Chaocipher. From today’s perspective, it’s likely
they weren’t being
truthful—perhaps to avoid offending Byrne Jr.
In
2009,
Israeli computer specialist Moshe Rubin launched a website to
collect information about the Chaocipher (Rubin, 2020). This
significantly
increased interest in the device. In 2010, Byrne Jr. finally relented:
he
published the workings of the Chaocipher, bringing the truth to light
after
more than 90 years. The Chaocipher turned out to be a system involving
two
cipher disks that had to be rotated after each letter during encryption
and
decryption (see Fig. 2.89). A unique feature was that the operator had
to
rearrange the letters on both disks before each read.
As
nearly all
experts had expected, the Chaocipher was far from
revolutionary. What Byrne considered unbreakable was actually solvable
if one
understood the method. Moreover, the constant rearranging of letters on
the
disks was extremely cumbersome.
So
the Chaocipher was not only less secure but also more unwieldy than the
Enigma,
which was developed around the same time. By the time Byrne published
his
autobiography in 1953, far superior encryption machines already
existed. In
1989, when Kruh and Deavours examined the device, computers had long
since
entered the field of cryptology. The hope of making money with a
two-disk
cipher machine was nothing more than a bad joke. In the end, the
Chaocipher was
just a 90-year-long misunderstanding. Fortunately, this skeleton from
the
cryptology closet has now been laid to rest.
While Schmeh’s overview is engaging, several factual
inaccuracies or oversimplifications appear in the text. These include
- “In his youth,
he was one of Ireland’s best chess players.”
- Byrne was certainly a talented chess player, but I have
not found independent evidence that he was regarded as one of
Ireland’s top players.
- “In 1973,
crypto‑historian Louis Kruh was looking for interesting topics for a
cryptology event and came across the Chaocipher.”
- In private correspondence with David Kahn (November
2010), Kahn wrote: “As
far as anyone else doing research on the Chaocipher, I found out after
"The Codebreakers" was published that Lou Kruh was interested in it. I
don't know how far he got or even what research he did.”
This suggests that Kruh’s interest dates back to
the late 1960s, earlier than the 1973 date mentioned.
- “In 2010, Byrne
Jr. finally relented: he published the workings of the Chaocipher,
bringing the truth to light after more than 90 years.”
- By 2010, Byrne Jr. had already passed away. The account
also omits the documented process of locating a Byrne family member and
ultimately connecting with Pat Byrne. While the precise path by which
the material surfaced may not be central to the cipher itself, the
description does not accurately reflect the historical sequence of
events. The Chaocipher papers surfaced in 2010 through archival work
and family contact, not through a decision by John Byrne, the son.
- “As nearly all
experts had expected, the Chaocipher was far from
revolutionary.”
- The historical context suggests a more nuanced view. The
concept of dynamic substitution was quite novel in the 1910s and did
not reappear prominently until electronic cipher modes emerged decades
later. No comparable mechanical system implementing dynamic
substitution appears in the cryptologic literature of that
era.
- “What Byrne
considered unbreakable was actually solvable if one understood the
method.”
- Byrne believed that even extremely large amounts of
ciphertext would not aid in solving the system -- an assumption that
later proved incorrect. However, it remains true that no method is
currently known for solving a single, long Chaocipher ciphertext
message without knowledge of the keys.
- “In the end,
the Chaocipher was just a 90‑year‑long misunderstanding.”
- If one interprets the situation as a misunderstanding, it
may relate to Byrne’s lack of awareness that autokey‑based
systems were not considered acceptable for military use.
AI-Generated
Podcasts Highlighting Chaocipher
Numerous websites offer AI-generated audios / podcasts as part of their
features or advertising pitch. Here I present two such AI
podcast audio files. Both audio files speak about my 2011
Cryptologia paper, "John
F. Byrne's Chaocipher Revealed: An Historical and Technical Appraisal".
The
first podcast, sent proactively in an email by academia.com,
presents a single narrator talking about the paper. The
presentation is a good one, and is a sample of what AI can do in this
area.
The
second podcast was generated by me using Google's NotebookLM,
a superb product for people who need to analyze existing papers and
textual sources. I uploaded my paper and requested an Audio
Overview. The result is two moderators, male and female,
discussing the paper. The technology is impressive, though
both podcasts mispronounce “Chaocipher.”
These AI‑generated summaries show how Chaocipher continues to appear in
new technological contexts, often in ways Byrne himself could never
have imagined.
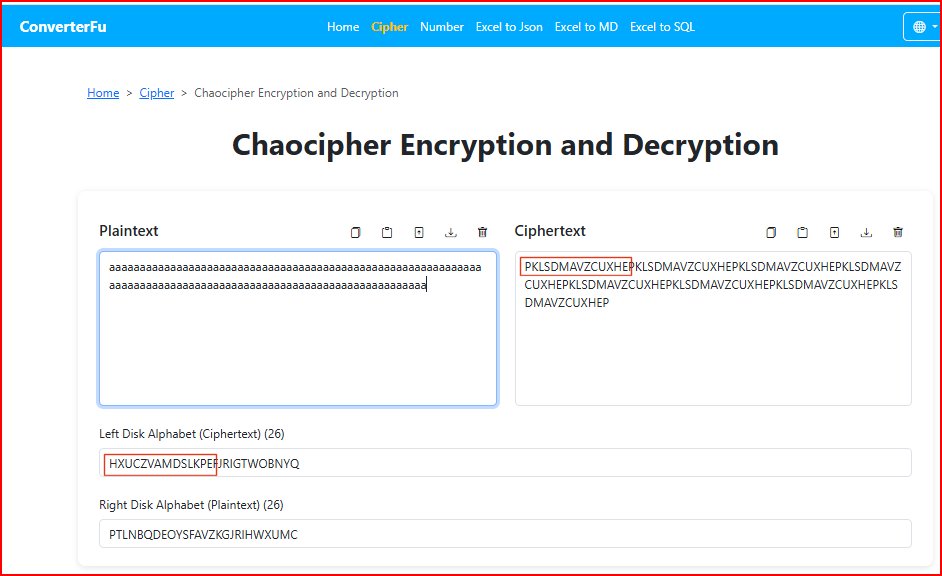
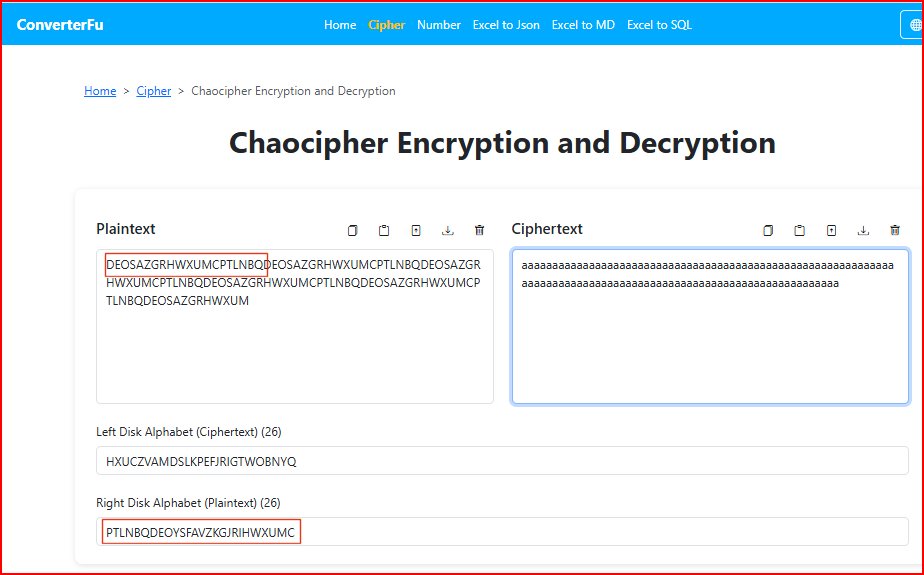
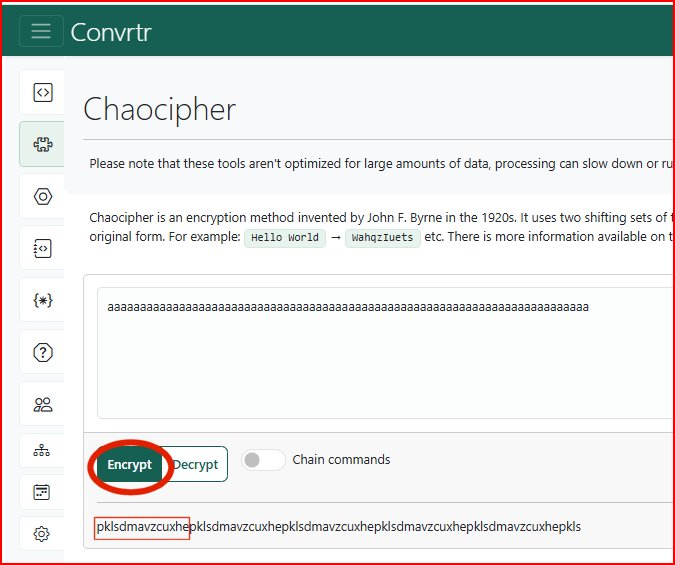
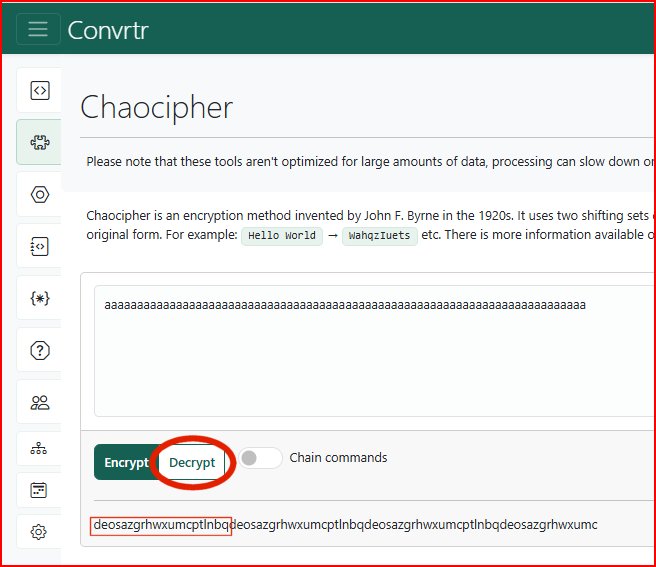
Chaocipher
Encryption / Decryption Websites
Here are two websites that provide users with an online Chaocipher
encrypt/decrypt tool:
These tools present you with an interesting experiment: encrypting /
decrypting a string of one character (e.g., "aaaaaaaa...").
Encrypting or decrypting a stream of identical characters
exposes a structural quirk of Chaocipher: the evolving alphabets become
partially visible. This does not immediately yield a practical attack,
since the cipher cannot be driven arbitrarily without plaintext, but it
does reveal internal state information that would normally remain
hidden.
Here we present encrypting and decrypting with a string of A's, for
both tools. Notice how portions of the left / right alphabet
sequences show up when encrypting / decrypting a stream of identical
characters.
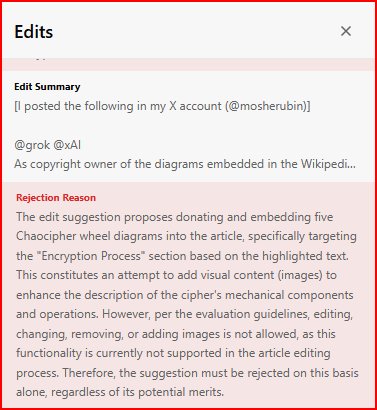
Grokipedia's
Webpage for Chaocipher
Grokipedia -- an AI‑generated encyclopedia powered by Elon
Musk’s Grok model -- automatically produces articles on a
wide range of topics. The Grokipedia
Chaocipher entry is an accurate and thorough exposition of
Chaocipher.
The one drawback with Grokipedia's process today is its inability to
integrate diagrams and pictures, due to copyright issues. I
contacted Grokipedia and offered my own Chaocipher diagrams free to
use, with no strings
attached. I received the following reply:
The
Irish Times: A Piece about John F. Byrne
Another modern reference to Byrne appears in a January 2017
Irish Times article
about John F. Byrne titled "Number
Seven’s Son – An Irishman’s Diary about
the cryptographer and friend of Joyce, John Francis Byrne".
The article is quite original, providing interesting tidbits
about Byrne and Joyce. I found the following of historical
value:
As the decades passed, he
remained admirably quiet about his former friend, whose work had
spawned an academic industry. But in 1953, he delivered the manuscript
of his memoir to a Joycean scholar in the New York Times, who at first
had no idea of his identity.
Joycean witness
After the visit, by
chance, the NYT man was having lunch with Frank O’Connor, who
told him excitedly that Byrne was the last important Joycean witness
still in the wild, and that the manuscript should be
protected zealously, or Joycean experts would “tear you
apart”.
This article is a reminder that Byrne’s life continues to
attract interest not only from cryptologists but also from literary
historians and journalists.
Byrne Genealogical Information
This section highlights recent genealogical findings and historical
sources related to John F. Byrne and his extended family
The
Byrne Identity: The Wicklow Background of Joyce's Cranley
Ken Hannigan has once again produced an invaluable paper about John F.
Byrne and his connection to Wicklow County in Ireland. This
paper, titled "The
Byrne Identity: The Wicklow Background of Joyce's Cranley",
was published in the Journal of the Wicklow Historical Society, Vol. 6,
No. 5, June 2023. The Byrne Identity examines the Wicklow
origins and family history of
John Francis Byrne (1880–1960) -- James Joyce’s
close friend and the real‑life model for Cranly in A Portrait of the
Artist as a Young Man. Drawing on parish records, burial registers, and
Byrne’s own autobiography, the article reconstructs the Byrne
and Fleming families’ migration from rural Wicklow to Dublin
and the social conditions that shaped Byrne’s early life.
The paper situates Byrne within the broader pattern of 19th‑century
Wicklow–Dublin migration, highlighting themes of poverty,
high child mortality, and shifting economic opportunities. It also
explores the family connections that brought Byrne to spend his
childhood summers in Wicklow -- experiences that influenced both his
personal identity and Joyce’s literary portrayal of him.
Hannigan concludes with generous remarks about The Chaocipher Clearing
House:
"Thanks
once again to Moshe Rubin for sharing the results of his indefatigable
investigations into J.F.Byrne and his Chaocipher.
Moshe’s website, The
Chaocipher Clearing House (
http://chaocipher.com)
is an amazing
collaborative online resource and has been used extensively in the
preparation of this and the previous article on Byrne. It is the
monument that Byrne might have craved had he been able to envisage it
–
and he probably did."
John
F. Byrne Family Tree in WikiTree
WikiTree provides a valuable family tree
about John F. Byrne. The WikiTree entry is
especially useful because it consolidates primary sources -- census
records, birth registries, and passport applications -- into a single,
well‑organized profile. Of special interest are the
references on that page:
John
F. Byrne and Gertrude Rodman: New York City Marriage Listing
As a Catholic, Byrne did not obtain a civil divorce from his first
wife, Mary Alice (née Headen) Byrne. For
years, his paramour, Gertrude
Rodman, lived in the same household together with Byrne and Mary.
Some online sources have wondered if Byrne ever
married
Rodman. The following links to the online New York City Marriage Index
Registry for 1958 prove that he indeed did:
Records indicate that Byrne married Gertrude Rodman in 1958, despite no
evidence of a prior divorce from Mary Alice. Byrne's
son John (1929-2008), the husband of Patricia
(Neway) Byrne, was Gertrude's biological son.
Mary
Alice (Headen) Byrne's grave
Here is a link to the gravesite
of John F. Byrne's first wife, Mary Alice (née Headen) Byrne.
Patricia
Byrne (née Neway) Obituary
TheatreAficionado.com is a small, niche website focused on
theatre and performing arts. In 2012 it featured an
obituary of Patricia (née Neway) Byrne
(1919-2012),
the wife of John Byrne and John F. Byrne's daughter-in-law.
TheatreAficionado.com
featured an obituary
for Patricia (née Neway) Byrne (1919-2012), an
acclaimed opera singer and the wife of John Byrne
(1929–2008). The obituary provides additional personal
context about the Byrne family’s later years.
These genealogical sources continue to shed light on Byrne’s
personal history, offering a fuller picture of the family context
behind the Chaocipher story
Copyright (c) 2009-2026 Moshe
Rubin
Created: 19 April 2026
Last Updated: